Cyberattacks have become a constant threat in today’s digital age, putting every internet user at risk. Among these threats, botnets stand out as a powerful and dangerous tool in the hands of hackers.
A botnet is a network of malware-infected devices controlled remotely to execute malicious activities. These networks can hijack numerous internet-connected devices to launch large-scale attacks, such as stealing data or disrupting online services.
In this article, we will explain what is a botnet, the types of botnet attacks, how it works, and how you can prevent yourself from a botnet attack.
Ready? Let’s get started!
What is a Botnet? — A Brief Introduction
A botnet is a network of devices, such as computers, smartphones, or IoT devices, infected by malware and controlled remotely by a cybercriminal. These devices, often referred to as “bots” or “zombie devices,” operate under the control of an individual known as the “bot herder” or “botmaster.”
Once compromised, these devices can be used to carry out various malicious activities, all coordinated from a central point. The bot herder can instruct the infected devices to perform large-scale attacks or tasks that would otherwise be difficult to execute with a single device. Given the scale of many botnets, which can consist of millions of bots, attackers can cause significant damage or disruption.
Some of the common uses of botnets include:
- Distributed Denial of Service (DDoS) Attacks: Flooding a target’s system with traffic to overwhelm its resources and disrupt normal operations.
- Sending Spam Emails: Using the network of infected devices to send large volumes of unsolicited emails, often for phishing or malware distribution.
- Cryptojacking: Exploiting the computing power of infected devices to mine cryptocurrencies without the owners’ consent. Not to be confused with Clickjacking.
- Data Theft: Harvesting sensitive information like login credentials, personal details, or financial data.
How Does a Botnet Attack Work?
Botnets enhance the scope, speed, and effectiveness of cyberattacks, allowing hackers to launch widespread campaigns using compromised devices. These botnets evolve and grow as the bot-herder manipulates and updates them. Infected devices, known as “zombie computers,” operate under the bot-herder’s control, carrying out tasks without the user’s knowledge.
A botnet attack typically unfolds in three stages:
Stage #1: Finding and Exploiting Vulnerabilities
The hacker first identifies a vulnerability in a device, which could be caused by a flaw in software, applications, or websites. These weaknesses might also result from human error. Attackers may use online messages, emails, or phishing tactics to trick users into downloading malware or visiting malicious sites.
Stage #2: Deploying Malware
Once the hacker gains access, they deploy malware to infect the device. This can be done through methods like Trojan viruses hidden in email attachments, deceptive pop-ups, or “drive-by downloads” from compromised websites. Hackers may also use social engineering to convince users to install malware unknowingly.
Stage #3: Activating the Device and Launching the Attack
After the malware infects the device, the bot-herder organizes the compromised machines into a network. This allows the attacker to remotely control the devices and initiate larger-scale operations. Infected devices, now part of a botnet, can be used to carry out various malicious tasks, including:
- Collecting personal data from users
- Monitoring user activity
- Reading and modifying system files
- Installing and running unauthorized applications
- Sending data and files
- Searching for vulnerabilities in other devices
With these capabilities, a botnet becomes a powerful tool for hackers, enabling them to execute a wide range of attacks efficiently.
Real-Life Examples of Botnet Attacks
Botnets have facilitated some of the most significant and damaging cyberattacks in recent history. Below are examples of infamous botnets that have caused widespread harm through various malicious activities:
- GameOver ZeuS
First identified in 2011, GameOver ZeuS operated as a peer-to-peer botnet designed to steal sensitive information such as banking credentials and login details. It infiltrated web browsers, altered web traffic, and intercepted confidential data from online platforms like banking websites. In addition to data theft, GameOver ZeuS distributed other types of malware, including ransomware, amplifying its destructive impact.
- Mirai
Discovered in 2016, Mirai targeted Internet of Things (IoT) devices like routers, security cameras, and smart gadgets. This botnet exploited weak or default credentials to infiltrate vulnerable devices and use them in large-scale Distributed Denial of Service (DDoS) attacks. Mirai has since evolved, spawning more sophisticated IoT-based botnets such as Reaper.
- ZeroAccess
Active around 2011, ZeroAccess is a Trojan that specifically targets Windows systems. It employed rootkit techniques to evade detection and forcibly recruited devices into its botnet. ZeroAccess was heavily utilized for cryptojacking and fraudulent ad-clicking activities. Although its influence has waned, remnants of this botnet remain active today.
- Emotet
Emotet emerged as a highly adaptable botnet capable of stealing sensitive information, spamming, and delivering other malware payloads. Although it was dismantled in early 2021, Emotet resurfaced in 2023, steadily regaining its reach and posing a renewed threat to cybersecurity.
These botnets highlight the serious risks posed by such networks, demonstrating their capacity to disrupt systems, steal data, and compromise devices on a massive scale.
Most Common Types of Botnet Attacks
Botnets are versatile tools that cybercriminals use to launch large-scale attacks, exploiting infected devices for malicious purposes. These attacks can overwhelm systems and cause significant harm. Here are some of the most common types of botnet attacks:
- Distributed Denial-of-Service (DDoS) Attacks
DDoS attacks use botnets to flood a target’s website or online service with massive amounts of traffic, overwhelming the system and causing it to crash or become unavailable. The attacker may demand a ransom to stop the attack, or the motive could be financial, personal, or political. DDoS attacks can lead to customer dissatisfaction, loss of revenue, and are often challenging to mitigate.
- Email Spam and Phishing
Spam botnets can send billions of unsolicited emails daily. These emails often carry malware to spread the botnet further, or they may deceive users into giving away sensitive information. Phishing campaigns impersonate trusted entities to trick individuals into revealing their credentials, such as banking or email login details.
- Ad and Click Fraud
Click fraud uses botnets to create fake web traffic, manipulating advertising metrics. In ad fraud, bots inflate views or clicks on online ads, benefiting the fraudster or boosting a website’s apparent popularity. This fraudulent activity can lead to financial loss for advertisers and distort performance data.
- Brute Force and Targeted Intrusions
Botnets increase the effectiveness of brute force attacks, where automated programs repeatedly attempt to guess passwords or break into accounts. Botnets also execute dictionary attacks and credential stuffing to exploit weak or reused passwords, gaining unauthorized access to valuable data or networks.
- Financial Breach
Financial botnets are designed to steal sensitive payment information, such as credit card details, from users. These botnets can directly target individuals or organizations, draining funds or enabling further financial crimes.
Botnets are not only dangerous in their own right but also serve as powerful tools for executing secondary cybercrimes on a massive scale. These attacks can lead to data theft, service disruptions, and significant financial losses.
Botnet Architecture: How Botnets Are Built?
Botnet architecture varies depending on how the network is structured and controlled. The two main models for botnets are client-server and peer-to-peer (P2P), and many botnets use a combination of both approaches to maximize efficiency and resilience.
#1: Client-Server Model
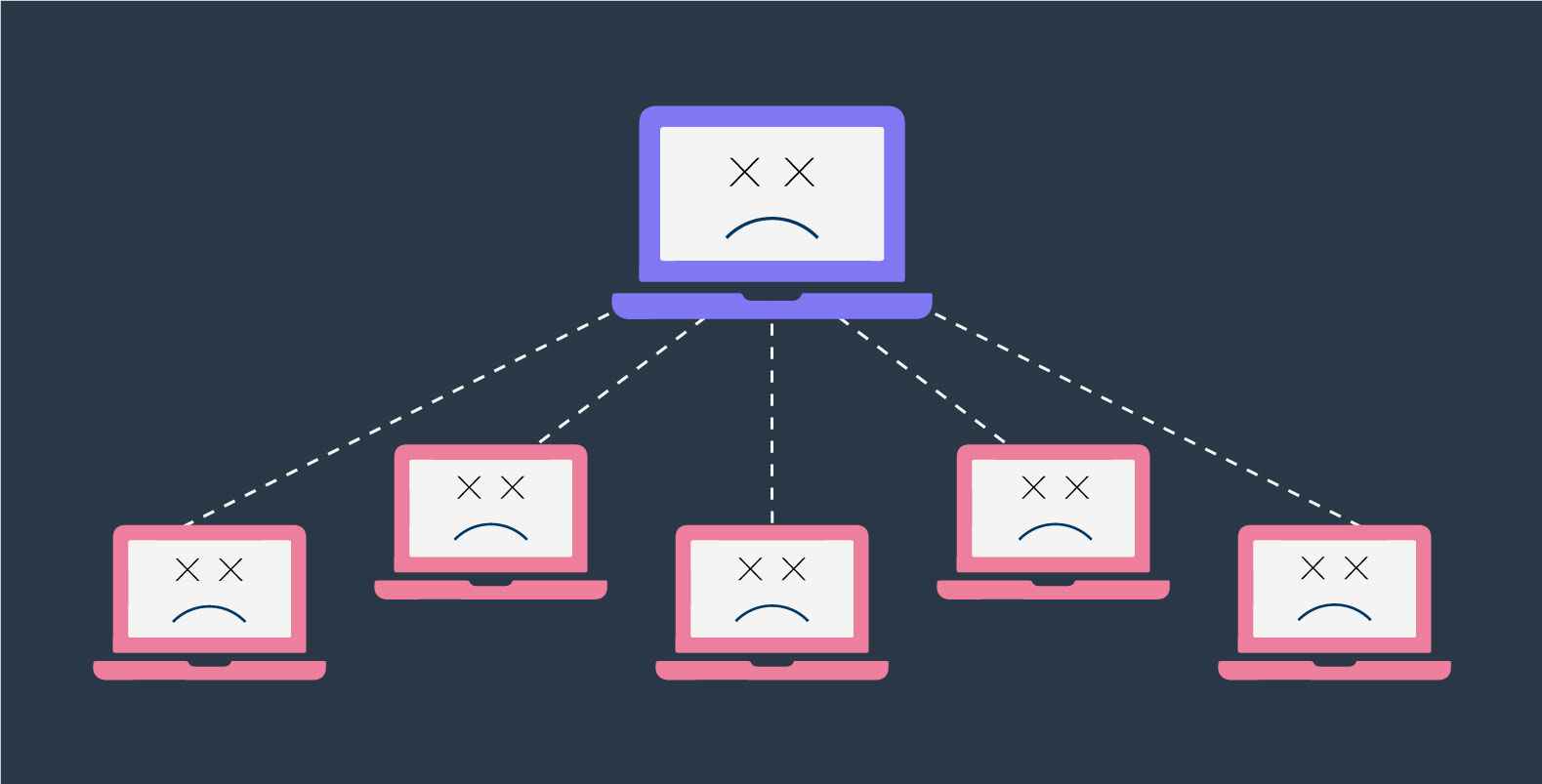
In the client-server model, the botnet operates in a centralized manner, with a single command-and-control (C&C) server managing all the infected devices. Once a device is compromised, it connects to the C&C server to receive commands, such as instructions to launch attacks or infect other devices. The hacker or bot herder controls the entire botnet from this central server.
Client-server botnets often use different network topologies to organize their structure:
- Star Topology: All infected devices (bots) connect to a central hub. The hub distributes data and instructions to each device in the network, creating a straightforward communication channel.
- Multi-Server Topology: Similar to the star model but with multiple servers handling communications between bots, making the network more resilient and scalable.
- Hierarchical Topology: In this model, a centralized server manages communication, but the bots handle their own communication with lower-level bots in the hierarchy. This allows for better distribution of commands across the botnet.
#2: Peer-to-Peer (P2P) Model
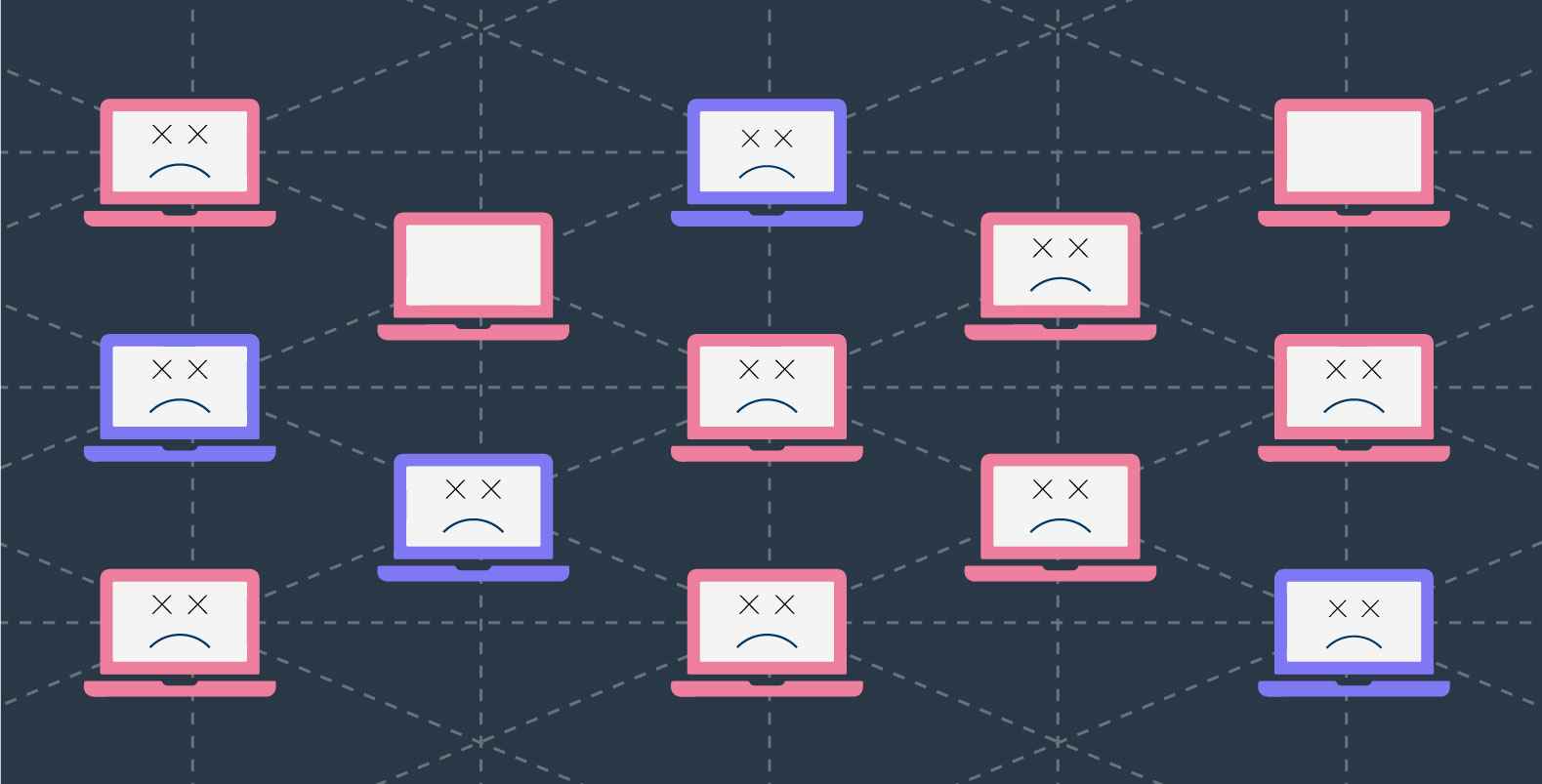
In contrast to the client-server model, P2P botnets are decentralized and do not rely on a single command-and-control server. Instead, each infected device in the botnet acts as both a client and a server. The malware is replicated across all systems, and each bot can share commands and data with other bots in the network.
P2P botnets are more resilient to attacks since there is no central server to target. Each bot maintains a list of trusted devices and can share updates or commands with nearby nodes. This decentralized structure makes it harder for authorities to dismantle the network. However, because of this decentralization, P2P botnets are more vulnerable to hijacking, so attackers often use encryption to protect communications and prevent unauthorized access.
The key advantage of the P2P model is the absence of a single point of failure. While the client-server model relies on the central server, which can be taken down to dismantle the botnet, a P2P botnet remains operational even if some of its nodes are compromised.
How to Protect Yourself From a Botnet Attack
Botnet attacks pose serious risks to individuals, businesses, and online ecosystems. Implementing these five effective strategies can help you reduce vulnerabilities and protect your devices:
#1: Keep Software and Systems Updated
Hackers often exploit outdated software to infiltrate systems. Regularly update your operating system, applications, and devices to protect against known vulnerabilities. If automatic updates are not an option, set a weekly schedule to manually update all software, ensuring your devices have the latest security patches.
#2: Use Advanced Botnet Detection Tools
Rely on professional detection tools to monitor and identify botnet activities in real time. Choose solutions that utilize AI and machine learning for behavior-based analysis, as traditional signature-based methods may fail to detect sophisticated botnets. Opt for tools that analyze extensive data to identify threats with precision.
#3: Educate Users and Employees About Phishing Risks
Phishing attacks often serve as the entry point for botnet malware. Train employees and users to recognize and avoid phishing attempts. They should:
- Avoid opening email attachments or clicking links from unknown or suspicious senders.
- Verify sender identities and email addresses before interacting with messages.
- Use reliable antivirus software to scan email attachments automatically.
#4: Create Strong, Unique Passwords
Weak passwords can easily expose devices to attacks. Use complex, unique passwords for every account, including administrative ones. Avoid reusing passwords across multiple platforms to minimize risks if one account is compromised.
You can further enhance your login security by replacing your common login URL with a more confidential one. For instance, you can easily access a WordPress login page by adding /wp-login.php/ ahead of the website URL. You can make it more confidential by using a plugin such as All-in-One Login.
#5: Install Robust Anti-Malware Software
Since botnets rely on malware to infect devices, installing strong anti-malware software is essential. Select a solution capable of detecting and neutralizing botnet malware and similar threats. Regularly update the software to keep up with emerging vulnerabilities and attack methods.
By following these practices, you can significantly reduce the likelihood of falling victim to botnet attacks and keep your devices and systems secure.
???? If you own a WordPress site, then check out our blog ???? 12 WordPress Security Best Practices to Consider.
To Sum It Up
Botnets represent a serious threat in today’s digital landscape, enabling cybercriminals to execute large-scale attacks, steal sensitive data, and disrupt online services. Understanding what is a botnet, how botnets operate, and the types of attacks they launch is crucial for staying protected.
By keeping software updated, using strong passwords, and employing advanced security tools, you can significantly reduce the risk of falling victim to these malicious networks.
Remember that proactive measures and awareness are your best defenses against evolving cyber threats.
Lastly, to strengthen your website’s security, try the Password Protected and All In One Login plugin together for an extra layer of protection against unauthorized access.